[ad_1]
This article is also available in German.
The Australian company Vmoto sells scooters and motorcycles with battery-electric drives under the Supersoco brand. Mostly installed at the factory: A GPS tracker connected by cellular network including a vehicle interface that delivers data to the Supersoco app via the manufacturer’s server. It shows the users the traction battery status, the position, the odometer, the phone number of the associated account and more.
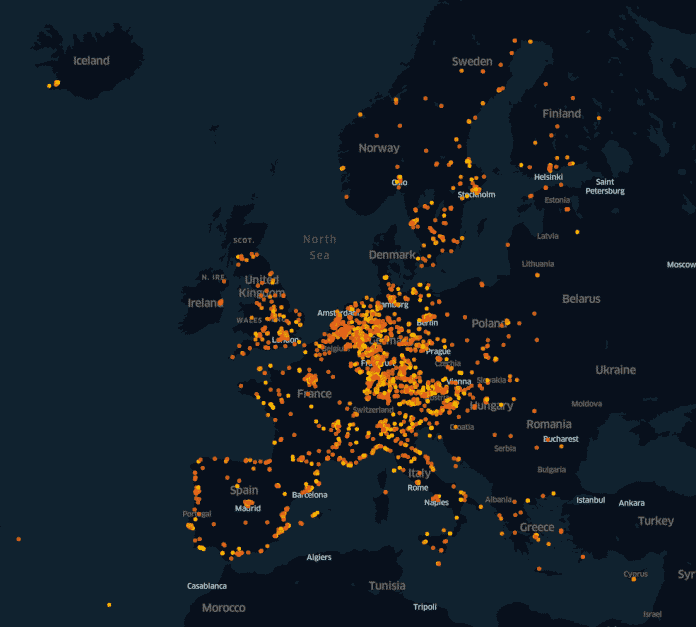
The IT security company “VTRUST” has now found a serious security gap in the application interface used and the vehicle registration process when investigating the Supersoco app. Despite the lack of authorization, the gap enables unrestricted readout of third-party vehicle data. It does not matter whether the owners concerned have registered their vehicle; regardless of this, the data is sent to the manufacturer’s server and saved. This was first noticed on the motorcycle of a VTrust employee. In order to rule out that there were only a few vehicles with a fault, the company carried out a proof of concept, which enabled access to several thousand vehicle data sets, primarily distributed across Europe.
The data set contained both registered and non-registered vehicles, as well as data sets over three months old, which, according to the manufacturer’s data protection declaration, should no longer exist. The c’t material shows that unauthorized access to all vehicles on the market that are equipped with a GPS tracker is possible at any time – including all conceivable scenarios for the use of this data, such as the creation of movement profiles. The data set with around 3500 vehicle data is probably only a fraction of the dimensions.
Communication chaos
After discovering the vulnerability, VTrust sought responsible disclosure and contacted the Supersoco importer for Austria and Germany, Hans Leeb GmbH in Austria. The only aim was to get in direct contact with the manufacturer in order to disclose technical details of the gap at the appropriate point. Despite several emails, phone calls and legal letters by fax and registered mail, the importer did not respond. Several direct e-mails to the manufacturer also received no response.
In March 2021, after almost four months of unsuccessful contact attempts, VTrust informed the magazine c’t about the security gap, demonstrated it and sent an anonymized data set. Thereupon c’t asked the importer and the manufacturer to comment on the lack of reaction and asked whether security gaps were already known. Attempts to make contact by telephone in Austria on the part of c’t always ended with the operator of the importer, as the person responsible was “just not available” or “in a meeting”. In a final attempt, c’t asked for a callback with additional information on the severity of the vulnerability, but it never came.
One day before the deadline set by c’t, the Supersoco data protection officer in Shanghai reacted: The problem described by VTrust had been investigated and nothing had been found. In addition, a GDPR review would have been carried out in 2019 together with TÜV Rheinland (Shanghai); However, the company did not say whether conformity was achieved. However, the e-mails from VTrust to Supersoco available to c’t contain no details about the vulnerability that Supersoco could have worked with.
VTrust told c’t that an email had also been received from Supersoco, but the manufacturer had not asked any further about the security gap and would instead take care of it itself. VTrust would also have no right to allow the press to publish anything, and Supersoco would reserve the right to take legal action in the event of damage. VTrust’s renewed offer to hold constructive talks went unanswered. When we asked what exactly Supersoco and TÜV had investigated, why there was no response for months and why they would not have simply asked for a free demonstration of the vulnerability from VTrust, the data protection officer also did not respond by the time we went to press.

High risk of theft
The security gap not only represents a major data protection problem for owners of Supersoco vehicles. It also promotes theft, because the GPS tracker has its own battery and reports to the server when neither of the two traction battery slots is occupied. They also supply the on-board electronics so that the alarm system does not work unless at least one traction battery is inserted. The owner can be notified of changes in position via the app; However, if the thief knows where the tracker is and removes it, there is quickly no trace.
Beispieldatensatz:{"account" : "49_157XXXXXXXX","deviceNo" : "03XXXXXXXXXXXXXX","deviceId" : XXXXX,"countryCode" : "DE","isWarnPush" : 1,"historyLocusSwitch" : 1,"userId" : XXXXX,"nowElec" : 34,"endurance" : 34,"gsm" : 2,"gps" : 5,"bindStatus" : 1,"latitude" : 49.XXXXX,"longitude" : 11.XXXXX,"powerStatus" : 0,"voltage" : 4,"loginTime" : "24/03/2021 00:11AM","lastGpsTime" : "24/03/2021 00:12AM","createTime" : "09/05/2019 03:54AM","status" : 1,"title" : "Lose connection with the battery","statusDesc" : "Your device number:03XXXXXXXXXXXXXX,Your battery has been plugged out or circuit-breaker turned off,please check the vehicle information","accumulativeRim" : 0,"sleep" : 0,"mileages" : 875.007220159274}
Owners of Supersoco two-wheelers currently only have to contact their service workshop, have the GPS tracker removed and optionally replace it with tracking hardware of their choice. The app functionality will then be omitted, but the reduced risk of theft and better data protection should far outweigh this.
At the same time as the publication of this article, c’t, in consultation with VTrust, drew the attention of the responsible German and Austrian federal authorities as well as the data protection officer of the European Union to the case.
(amo)
[ad_2]
